News tagged ‘security’
Steve Jobs' "Venus" is no longer impounded

Last Friday, it was noted that the Jobs family's new yacht had been confiscated by the authorities of the Netherlands as a result of the dispute over design payment in favor of the famous French designer Philippe Starck. Stark asserted that he should have received the payment in the amount of 9 million euros for designing yacht, however the Jobs family reported that agreed rate was equal to 6% of the yacht valued in the 105 million euros. Stark said that his fee will be lower by about 3 million euro.
Apple Releases iOS 6.0.2 for the iPhone 5 and iPad Mini
Apple has just released iOS 6.0.2 for the iPhone 5 and iPad mini.
iOS 6.0.2 Software Update
This update contains improvements and bug fixes, including:
• Fixes a bug that could impact Wi-FiFor information on the security content of this update, please visit this website: http://support.apple.com/kb/HT1222
You can update on the device itself, in iTunes or download firmware files here:
- 6.0.2 (iPhone 5 GSM):
- 6.0.2 (iPhone 5 CDMA):
- 6.0.2 (iPad Mini Wi-Fi):
- 6.0.2 (iPad Mini GSM):
- 6.0.2 (iPad Mini CDMA):
Apple Releases iOS 6.0.1 for iPhone, iPad and iPod Touch
Apple has released iOS 6.0.1 to iPad, iPad Mini, iPhone and iPod touch users. You can download the update by connecting your device to iTunes to download or via OTA update. Apple says that this update includes various improvements and bug fixes.
Fixes a bug that prevents iPhone 5 from installing software updates wirelessly over the air
Fixes a bug where horizontal lines may be displayed across the keyboard
Fixes an issue that could cause camera flash to not go off
Improves reliability of iPhone 5 and iPod touch (5th generation) when connected to encrypted WPA2 Wi-Fi networks
Resolves an issue that prevents iPhone from using the cellular network in some instances
Consolidated the Use Cellular Data switch for iTunes Match
Fixes a Passcode Lock bug which sometimes allowed access to Passbook pass details from lock screen
Fixes a bug affecting Exchange meetings
For information on the security content of this update, please visit this website: http://support.apple.com/kb/HT1222
If you have an iPhone 5, the updater will download an app first that enables OTA updates then it will download 6.0.1.
Direct links to iOS 6.0.1 are available here.
 Leave a comment, read comments [2]
Leave a comment, read comments [2]
Pentagon plans to purchase over 162K Apple iOS and Android devices
The United States Department of Defense plans to revise and expand its security infrastructure by replacing BlackBerry devices with iPhone and the iPad from Apple, as well as with some selected smartphones and tablets running Android OS. The plan was revealed in the document published in this month which offered the solution to ensure the safety of Apple and Android devices, BlackBerry and Windows products, reports Bloomberg.
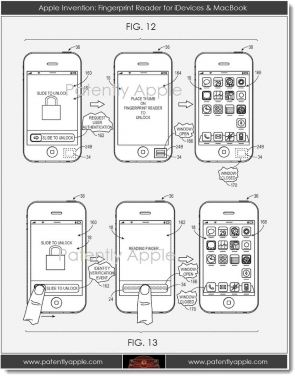
Apple Patent Describes Electronic Window That Hides Biometric Sensors
With Apple’s purchase of a fingertip sensor firm AuthenTec for $365 million, there has been much speculation on how Apple might utilize the technology in its future devices. Today Patently Apple on a new Apple’s patent introducing an all-new unlock screen feature based on fingerprint technology.
Apple Plans To Work With Microlatch On Fingerprint Recognition Technology
While AuthenTec's board of directors is expected to approve to work together on integration of similar fingerprint recognition technology with mobile payments via NFC (near filed communications).
AuntenTec Will Stop Supplying Fingerprint Sensors To Non-Apple Customers in 2013
According to Korean website , fingerprint sensor company AuthenTec has notified many of its customers, including Dell, Lenovo, HP, Fujiitsu and Samsung, that it will stop offering its technology to them as of next year. In July Apple agreed to buy AuthenTec, and it is expected that AuthenTec's board will approve the acquisition in October.
Apple Announces New 4-inch iPod Touch And Multitouch iPod Nano
Today at its media event Apple updated the iPod touch lineup to a fifth generation model that includes the same 4" screen as the new iPhone 5. At only 88 grams and 6.1mm thin the new iPod touch is lighter than all previous iPod touch models. The new model incorporates the A5 processor.
Previously-Thought NFC Chip in iPhone 5 is Earpiece Speaker
The latest pictures of the rumored next-generation iPhone published on Thursday by Sonny Dickson offer a look at a mysterious internal component located next to the earpiece. Some analysts suggested that the unknown component could be the NFC chip. But last week, the well-connected Jim Dalrymple of The Loop reported that Apple's next iPhone will not feature NFC technology, sometimes known as radio frequency identification, or RFID.
 Leave a comment, read comments [1]
Leave a comment, read comments [1]
New Java vulnerability affects Macs
Researchers announced on this Monday that they had discovered vulnerability in Java 7. Hackers can use the bug to compromise any system through a web browser running the latest Java software, reports Tod Beardsley, engineering manager for open-source testing framework.
Apple Temporarily Stopped iCloud Password Resets Over The Phone
of reporter Mat Honan whose iCloud account was hacked, which resulted in the wipe of his MacBook Air, iPad and iPhone. Wired reports:
How Hackers Gained Control Of Reporter’s iCloud Account
On Sunday Wired reporter Mat Honan that hackers gained control of his account at iCloud and remotely wiped his MacBook Air, iPad and iPhone and as well as further gained access to his Gmail and Twitter accounts. Today he the exact process of the hacking.
Apple to Buy Mobile Security Company AuthenTec for $356 Million

Reuters reports that Apple has reportedly reached a deal to purchase AuthenTec, a security company best known for creating fingerprint sensors, for $356 million. The acquisition agreement was approved with unanimous consent by AuthenTec's board this week, according to Bezinga. The deal is not yet finalized because it requires approval from the majority of outstanding shares of the company's common stock, among other final steps.
Apple Released OS X Mountain Lion Priced At $19,99
Today Apple has launched its new OS X Mountain Lion to the public. The new operating system is priced at $19.99 and can be purchased exclusively on the Mac App Store.
OS X Mountain Lion offers many new features and improvements to the Mac, including iMesage support through the Messages app, Notification Center, Reminders and Notes support via iCloud, Dictation, Game Center, improved sharing capabilities, enhanced security with Gatekeeper, Power Nap and more.
Apple Already Pursuing Minor Expansion at North Carolina Data Center
In March, Apple filed an application for permit to build a "tactical data center" to be located at the site of the company's existing data center in Maiden, North Carolina. Such tactical data center is expected to locate at the relatively small area of 20,000 square feet. The Hickory Daily Record that discovered Apple’s filling now issued a new report revealing more details on Apple's plans.