News tagged ‘security’
Apple Vice President of Global Security John Theriault departs company following lost iPhone 4S investigation
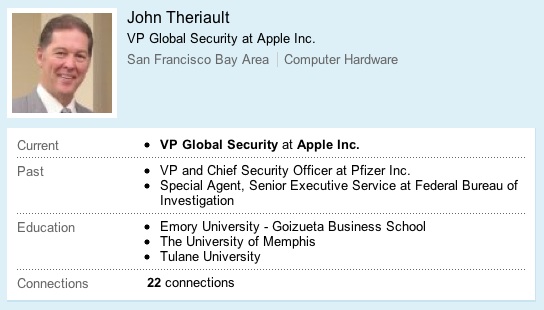
A large number of Apple senior executives have left the company this year. And Apple’s vice president of global security John Theriault is one of them. We’ve heard that the reason for his departure could be the lost iPhone 4S prototype, while the official reason is retirement.
In July, an Apple employee lost a prototype of the new iPhone at the Cava22 bar in San Francisco. Following the loss of the prototype device, Apple security personnel being escorted by San Francisco police visited a home to where the device had been traced. Apple security officials reportedly posed as police officers in their search of this prototype iPhone. Apple and the SFPD may face a lawsuit over the matter, as the resident claims that he was threatened by the police and was not informed that Apple's security officials were not actually officers.
Theriault, a former FBI agent and Pfizer vice president, joined Apple in 2007. Theriault was responsible for all of the Apple’s security operations and led an anti-counterfeit team in 2008 in a fight against China’s growing counterfeit product market.
Apple Pushed Implementation Of Sandboxing Requirement In Mac App Store To March
Among the user-interface changes in OS X 10.7 (Lion), Apple also included a number of changes in the security model that may affect customers of Mac App Store in the near future. One of them is a sandboxing system which can prevent third-party apps from causing damage.
Apple released iOS 5.0.1 beta to developers
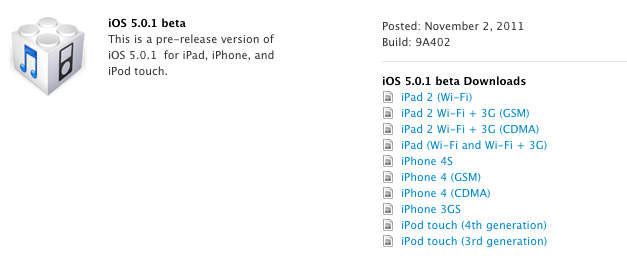
Apple has just relased iOS 5.0.1 (9A402) to developers. The new update features battery life fixes, multitasking gestures on the original iPad, improves Voice recognition for Australian users, and features other bug and security fixes. The update is about 811MB. Developers can download it from the Developer Center.
iOS 5.0.1 beta also introduces a new way for developers to specify files that should remain on device, even in low storage situations.
Changelog:
Read the rest of this entry »
New Mac OS X Trojan horse hijacks GPU, spies and steals
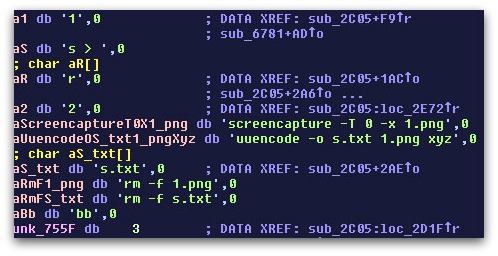
A security firm Sophos, released a report which claims that a new Trojan horse was found to be hidden in a Mac OS X application, Graphic Converter 7.4.
The new Trojan called DevilRobber can steal sensitive user data, usernames and passwords, and take control of the computer’s GPU to generate Bitcoins, a form of currency used online, and is capable of spying on users by taking screenshots of their activity and sending the images online. DevilRobber, also known as "OSX/Miner-D," also runs scripts that can copy information “regarding truecrypt data, Vidalia (TOR plugin for Firefox), your Safari browsing history, and .bash_history” to a dump.txt file. The malware is also able to search for “pthc” files (the term means pre-teen hardcore pornography). And probably that is one of its secondary features to find traces of child abuse on affected computers that could be used against owners of such computers, for example.
Sophos suggests that users may notice that their computers have been attacked by the Trojan. This may affect overall computing performance when the Trojan steals GPU resources. The company asks users not to download software from unreliable sources. Though, common anti-virus programs are able to detect the Trojan.
 Leave a comment, read comments [1]
Leave a comment, read comments [1]
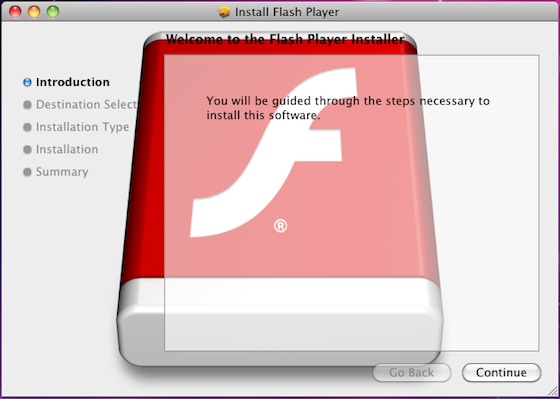
Modified Trojan Disables Auto-updating Function Of Anti-Malware Tools In OS X
Last month it was reported that a new trojan known as Flashback.A has appeared and masqueraded as a Flash Player installer. Though Apple has continuously updated its XProtect.plist to detect this malware, security firm F-Secure has (via ) that a modified version of the trojan horse that disables the auto-updating function of Apple’s anti-malware tools has surfaced.
Amazon announced iPad killer: Kindle Fire

Today Amazon announced their tablet called Kindle Fire. It has 7" IPS display, custom android OS, weights 413g, has 8Gb of storage, Wifi. Unfortunately it does not have 3G. The price is attractive though - $199. Shipments start November 15.
We are not sure that this device can be a real iPad killer. However it will definitely compete with other Android tablets, like Blackberry Playbook, HP Touchpad and others.
More specs:
 Leave a comment, read comments [3]
Leave a comment, read comments [3]
Skype Released Updates For Its Native iPad, iPhone and iPod touch Apps
Today Skype updated its app for as well as for iPhone and iPod touch. Now the Skype app for iPad has Bluetooth connectivity on iPad 2 and a bugfix for security problems. Also the app can operate both on iPad and iPad 2. The program for iPhone/iPod touch also supports Bluetooth on the fourth-gen iPod touch, iPhone 3GS, iPhone 4.
Apple Updates Anti-Malware Tools to Address New Trojan Threat
Blurred screenshot of PDF file deployed by OSX/Revir.A
Late last week, a new trojan threat has targeted Mac users. It consists of two parts, with the first being a trojan downloader known as "OSX/Revir.A" that downloads and opens a PDF document containing "offensive political statements" written in Chinese, and installs a a backdoor known as OSX/Imuler.A that allows to get access to the user's machine.
When the backdoor is installed, it will set up a launch agent on the system that is used to continually keep the malware active on the system. It will then connect to a remote server and send the system's current username and MAC address to the server, after which the server will instruct it to either archive files and upload them, or take screenshots and upload them to the server.
Apple has quickly responded having updated its malware definitions for Snow Leopard and Lion systems so that they can recognize the trojan.
CNET has also reported that another trojan horse, known as OSX/flashback.A, has been discovered. The new trojan masquerades as a Flash Player installer to trick users into installing the package.
Kensington Announced Two New Security Products For iPad And iPhone
Kensington has a couple of security products for iPhone and iPad including lock mechanism SecureBack and intergrated alarm case BungeAir for iPhone.
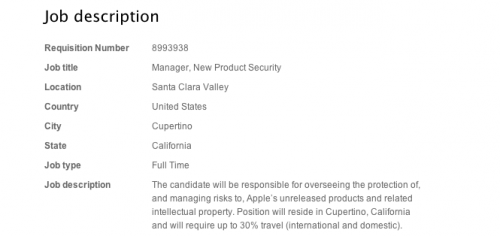
Apple Hunting For People To Beef Up ‘New Product Security’
After amazing lost of the iPhone 5 prototype, Apple seems to start worry about their forthcoming devices, having posted a job listing for two positions that are titled “New Product Security Managers”. Noteworthy to say, that these positions became available just a day after there appeared rumors claiming that Apple had lost the iPhone 5 prototype at a San Francisco bar. That’s probably somewhat of a coincidence, but it is obvious that the company does its best to protect future products and its intellectual property, describing the new jobs as follows:
The candidate will be responsible for overseeing the protection of, and managing risks to, Apple’s unreleased products and related intellectual property. Position will reside in Cupertino, California and will require up to 30% travel (international and domestic). The individual will collaborate with other security managers by contributing to, and managing execution of, strategic initiatives set forth by Director, Global Security.
Carriers Currently Testing iPhone 5 in Sealed Boxes
In June it was reported that the carries were testing the new iPhone 5. And now The Guardian offers some details on the carrier testing process, suggesting that Apple could be ready for September launch of the iPhone 5.
My carrier sources tell me that the boxes in which the new iPhone hardware is encased have been transported to carriers for testing. This is an important step in the release cycle for any phone. ... The next iPhones go for their testing inside locked and sealed boxes so that the carriers can carry out checks on their network compatibility in their labs. It's very high security, as you could guess; my understanding is that barely anyone inside the carriers gets to open those boxes, and even when they do the hardware is encased in a dummy body which means there's no clue to what the actual phone will do.
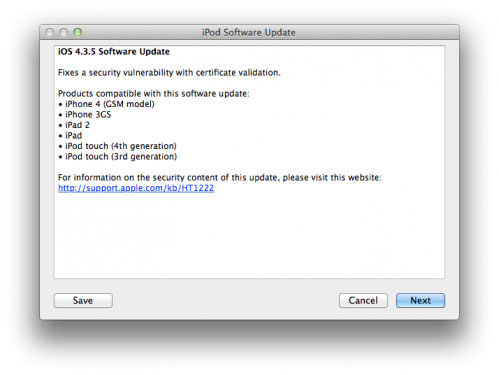
Apple Released iOS 4.3.5 for iPhone, iPad, iPod Touch
Apple released iOS 4.3.5 for the iPhone, iPad, and iPod touch. The new firmware fixes a security update with certificate validation. For Verizon iPhone owners Apple released iOS 4.2.10.
Products compatible with this software update:
- iPhone 4
- iPhone 3GS
- iPad 2
- iPad
- iPod touch 3G
- iPod touch 3G
You can update via iTunes or download using direct links here.
Not Only iPhone But Even Apple Store Can Be Faked
China is a home not only of fake iPhones, but also of fake Apple Stores. A fake Apple Store is shown on the pictures from (via ). This store is a complete fake with everything that the Apple Store has. It offers all from blue shirts with logos of Apple to name labels for the staff. This store features a light exterior with a luminous, white Apple logo shining in the most conspicuous place.
Apple released iOS 4.3.4 that blocks JailbreakMe exploit
Apple has released iOS 4.3.4 to block the PDF exploit used by comex in JailbreakMe utility. JailbreakMe can wireless jailbreak all devices on iOS 4.3.3.
iOS 4.3.4 Software Update
Fixes security vulnerability associated with viewing malicious PDF files.Products compatible with this software update:
• iPhone 4 (GSM model)
• iPhone 3GS
• iPad 2
• iPad
• iPod touch (4th generation)
• iPod touch (3rd generation)
For iPhone 4 Verizon Apple released iOS 4.2.9.
The official information is available here:
Mac OS X Lion Round Up
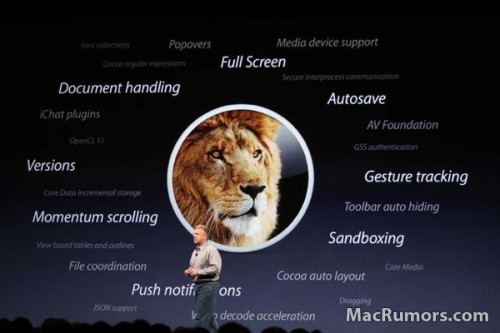
Mac OS X is almost 10 years, but it still continues to evolve and as Phillip Schiller claims "not because of hardware, but because of software." During yesterdays keynote Apple unveiled only ten of 250 new features in Mac OS X Lion.Some of the new features include Windows Migration Assistant, a new version of FileVault, built-in FaceTime and more.
Lion will be available only through App Store as a 4 GB download for $29.99. So you pay ones and may install the new software on all your machines. Little bit strange but App did announce an exact date of MacOS X Lion release.
"New" features that were announced during keynote, include: