In Response To Flash Player Trojan Apple Updates Anti-Malware Data
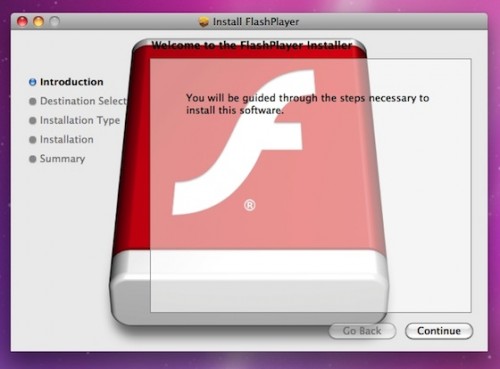
Since a raid on Russian payment processing company ChronoPay two month ago, there was not much work for malware defense system of OS X , but a new trojan horse did emerged earlier this month. to F-Secure, the trojan called "OSX.QHost.WB.A" disguises itself as a Flash Player installer and adds records to a file on the computer’s host to redirect users trying to visit some of Google sites. The server in Netherlands shows a fake webpage that is very similar to the real Google site.
When opening fake Google pages found by the search engine, people were redirected to pop-up windows loading some content, that was already destroyed at the time of malware detection, but supposedly it was some sort of advertisement. The threat was not serious, but inexperienced users facing the trojan didn’t understand what had happened with their computer and how to fix this routing problem.
In reaction to this issue, Apple earlier this week made necessary changes to its "XProtect.plist" file. This file contains definitions of malware for recognition and warning users in case of malicious downloads.
Originally anti-malware system could be updated only manually, and actually it was updated rarely only when larger updates of software occured. But in response to the MacDefender malicious activity earlier this year, Apple enable Mac OS X system to daily check for updates of this file to provide prompt reaction against malware.
Follow us on :
 Leave a comment
Leave a comment