News tagged ‘security’
iPhone iOS 4.1 Jailbreak Released from GeoHot, called LimeRa1n

Famous hacker Geohot is back and today he released the latest iOS 4.1 jailbreak. It is called LimeRa1n and supports iPhone 3GS, iPod Touch 3G, iPad, iPhone 4, iPod Touch 4G with iOS firmwares 4.0-4.1 and beyond. It can also hacktivate your device, so there is no need in phone SIM-cards and other tricks.
This software is still in beta and was updated 3 times in last several hours. So use with caution.
There is Windows version only for now. Geohot plans to release LimeRa1n for Mac and Linux soon. You can Download it here.
Some users report that they have jailbroken their iOS 3.2.2 iPads successfully with limera1n, while others report that they tried, but failed.
Do not forget to backup.
For many users of iPhone 3GS and iPhone 4 with iOS 4.0.2 now there is a hope to perform jailbreak using LimeRa1n and unlock using ultrasn0w. We recommend NOT to do it if you have not saved your SHSH keys. You can try, but if something goes wrong without SHSH keys you'll have to restore to iOS 4.1, and there is no unlock for iOS 4.1 (possibly forever). Just wait for PwnageTool utility.
DevTeam reported that Limera1n uses a different exploit than SHAtter, so they will not release SHAtter utility, they don't want let Apple fix both security holes. However they plan to release PwnageTool using the same exploit.
You can find our LimeRa1n tutorials tutorials:
Safari Updated to 5.0.2
A new updated browser Safari 5.0.2 has been released. It takes 40MB.
This update includes improved compatibility and security, including the following fixes and features:
• The problem preventing users from filling out web forms has been successfully fixed.
• The problem leading to the incorrect display of web content while viewing Google images with Flash 10.1, has been fixed as well.
• The encrypted connection to the Gallery of Safari Extensions has been established.
More information about the security on the content provided by the update, you can find out by visiting the website: http://support.apple.com/kb/HT1222
Download the application !
Apple seeds third Mac OS X 10.6.5 beta

Apple on Thursday seeded with developers the third beta of Mac OS X 10.6.5, its latest security and maintenance update for Snow Leopard, with just one known issue.People familiar with the latest build, reportedly known as 10H531, said the lone issue is associated with VMware. Having it installed can cause USB devices to not work when the Mac is awoken from sleep mode.
Those same people said Apple has asked developers to focus on a few key areas for the latest beta, including iCal, Mail, USB Devices, QuickTime, Time Machine and 3D graphics. The delta update is said to be a 557MB download.
Former Apple manager accused of hiding $125k in shoeboxes
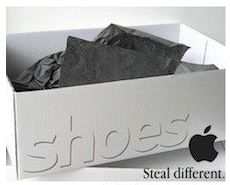 Paul Devine, the Apple supply manager charged with accepting kickbacks from overseas partners, allegedly had more than $150,000 in cash stashed in shoe boxes in his home when it was raided by federal agents. Moreover, the investigation had found “a significant number of overseas accounts and a significant amount of money”. The judge determined that Devine represents a potential flight risk if he is let out on bail before the foreign funds have been moved into the U.S.
Paul Devine, the Apple supply manager charged with accepting kickbacks from overseas partners, allegedly had more than $150,000 in cash stashed in shoe boxes in his home when it was raided by federal agents. Moreover, the investigation had found “a significant number of overseas accounts and a significant amount of money”. The judge determined that Devine represents a potential flight risk if he is let out on bail before the foreign funds have been moved into the U.S.
Earlier this month, Devine was arrested and charged with wire fraud, kickbacks and money laundering. Prosecutors have alleged that the Apple global supply manager used his security clearance to provide confidential information to the hardware maker's suppliers. Apple's partners then allegedly used the information to negotiate favorable contracts with Apple, and, the prosecution says, paid kickbacks to Devine. Devine is accused of accepting more than a million dollars from Asian suppliers.
Man Uses iPhone to Watch Live Video of His Home Being Burglarized

While on vacation, Vincent Hunter received an alert from his iCam iPhone app: Something had set off the motion detectors in his home. He used the app to access his security cameras, called 911, and helplessly watched a burglary unfold.
While Hunter's home security company had also contacted the authorities around the same time as he did, the man was still left watching two burglars leave his home before police officers arrived. There are no details about what was taken from the home and the burglars have not been caught.
The five dollar iCam iPhone app used by Hunter is somewhat similar to software you could install to monitor your security system while away from home, but there's something additionally frustrating seeming about pulling your iPhone out of your pocket to a devastating alert and watching the crime right there on the little screen.
Apple’s Supply Manager Earned $1M By Selling Company’s Secrets
New report published in the San Jose Mercury News reveals that recently Apple’s global supply manager Paul Shin Devine was accused by the US Internal Revenue Service and Federal Bureau of Investigation in a fraud scheme. It is claimed that Devine was using his security clearance to obtain confidential information about Apple’s upcoming products and provide it to the company’s suppliers. The latter then used the info to make favorable deals with Apple and after that paid Devine kickbacks. One of the suppliers was Andrew Ang from Singapore, who is also named in the indictment as an accomplice, as Devine was sharing his kickbacks with him.
To receive payments Devine held a series of accounts inside and outside the US. Payments were marked as “samples” so no attention was attracted. Bank accounts were registered under his and his wife’s names. It is reported that sometimes Devine received bribes on the meetings with suppliers in Asia.
Saurik released a PDF patch for older and already jailbroken iOS devices

As you may know, few days ago Apple had released a new version of iOS for all its mobile devices except first-generation iPhone and iPod touch, so owners of the latter are still not protected from a security flaw that allows hackers to obtain a remote control of their handsets. In fact, the latest compatible version for them is currently iOS 3.1.3.
But Saurik (who is known as a developer of Cydia) recently announced on the Dev-Team blog that he released a PDF patch that is compatible with any iOS version down to 2.x. It can be found in Cydia if you'll search for "PDF Patch". After installing it you can check if the patch is working properly with visiting jailbreakme.com page. After sliding the box to jailbreak you should only see the star background (and not a dialog box), which means you are no longer vulnerable.
Read the rest of this entry »
 Leave a comment, read comments [9]
Leave a comment, read comments [9]
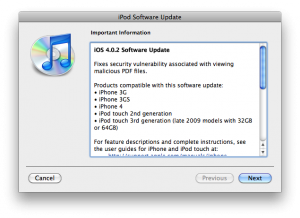
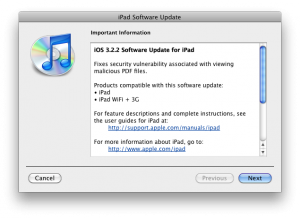
iOS 4.0.2 for iPhone, iOS 3.2.2 for iPad Have Been Released
Today Apple released patches for its iOS that address a security hole in Mobile Safari, which allowed users to jailbreak their iDevices. The PDF exploit they used also allowed hackers to gain remote control over the device with an iOS.
iOS 4.0.2 is available for:
- .
Apple did NOT release the patch for the first generation iPhones.
iOS 3.2.2 is intended to use on the .
You can update your device via the links above or simply by connecting your device to iTunes and clicking Update. But note, if you want to continue using jailbreak you should not update your handset/tablet and don't forget to backup your SHSH blobs.
Howto secure iPhone iOS: PDF exploit fix
There is a big a security hole in iPhone iOS. The device is insecure in a big and obvious way. You should be extremely careful of what sites you visit.
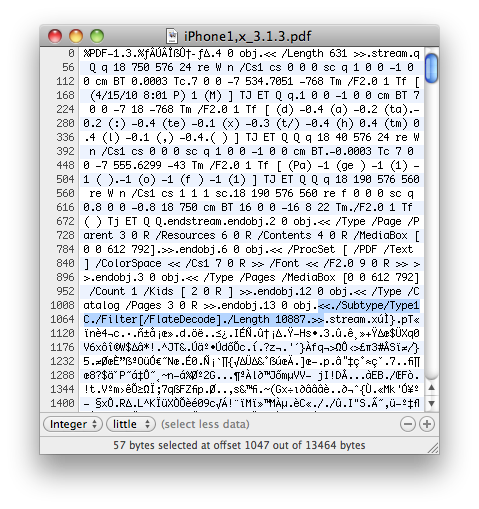
The FlateDecode vulnerability can be used when a PDF File is embedded within a Web page. Basically Safari tries to parse the PDF. And when it does it executes some code. Hackers can use this exploit to read and write iPhone data, get your contacts, sms, even delete something. So they can get all kinds to access your personal information stored on your iOS device.
Apple will fix it some day. Until then you need to take care of your iPhone security. There is a fix for that. It is available via Cydia for jailbroken devices. So you need to jailbreak in order to secure (funny isn't it?).
Apple investigates iOS vulnerabilities

Recently Vupen, which is a French security firm, posted an advisory that contained information about two critical security vulnerabilities in Apple's iOS. After a while hacker comex used these flaws to create a jailbreak, which is now widely known and available on JailbreakMe.com.
But according to Reuters, yesterday Apple decided to react and its spokeswoman Natalie Harrison revealed that the company is currently investigating Vupen's advisory. So it looks like these exploits are going to be fixed soon!
New Jailbreak for iOS Devices is Browser-Based
Starting today every owner of iPad, iPhone or iPod can easily jailbreak his device via browser on
The site was created in a week after decision of the Library of Congress (that operates the Copyright Office), which states that jailbreaking isn't illegal, though Apple claims it actually represents a threat to the stability and security of the company's devices. Apple also says that jailbreaking voids the warranty, but such an action can be easily undone by resetting a device to the default factory settings.
Site JailbreakMe.com easily became a trending topic in Twitter after its announcement on RedmondPie.com. The jailbreak itself was created by hacker comex, and the website was done by chpwn and westbaer.
 Leave a comment, read comments [2]
Leave a comment, read comments [2]
Android Data Theft App Was Downloaded By Million Users

At the Black Hat security conference, which is being held this week, research firm Lookout told about malicious application that was found in Google's Android Market. It was collecting private data (such as phone's SIM card number, text messages, browsing history, voice mail password and subscriber identification) and then sending it to a web site imnet.us, which is owned by an unknown person in Shenzhen, China.
According to VentureBeat report, written by Dean Takahashi, an app was claimed to load custom background wallpapers and was submitted by Jackeey Wallpaper.
Read the rest of this entry »
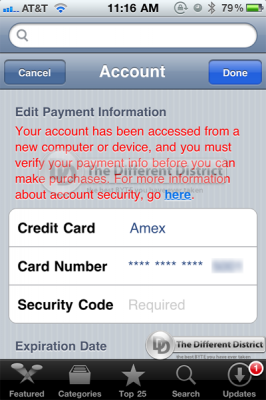
Apple Improved iTunes Store Security
As you remember, few weeks ago iTunes Store was hacked and the top list of the Books category had been filled with a bunch of obscure books. That was achieved by a number of unauthorized charges that were made on accounts of several iTunes users, who eventually lost few hundred dollars. In turn Apple deleted developers who were found to use the fraudulent purchases.
These days Apple added new layer of security which now require every user to enter the security code of their credit card each time they register a new device or computer with their account, according to Different District blog. So if earlier malicious user just needed to guess a password for the account in order to receive and/or resell the acquired information to fraudulent buyers, after Apple’s security innovation it will require more efforts to do that.
Old Wi-Fi-enabled iPhone Will Finally Go On Sale in China
According to The Wall Street Journal, last week Chinese Telecommunication Equipment Certification Center approved Wi-Fi enabled iPhone to be put on sale soon in China. The problem is that on the accompanying picture it is clearly seen that the approved device is the iPhone 3G or 3GS, but certainly not the iPhone 4.
Apple’s smartphone went on sale last year, but it was Wi-Fi disabled because technology's standard was temporarily banned by the Chinese government. In May 2009 the ban was relaxed.
Read the rest of this entry »
Official iOS 4 changelog from Apple

Here's an official changelog for recently released iOS 4 for iPhone and iPod Touch:
This update contains over 100 new features, including the following:
• Multitasking support for third-party apps*
– Multitasking user interface to quickly move between apps
– Support for audio apps to play in the background
– VoIP apps can receive and maintain calls in the background or when device is asleep
– Apps can monitor location and take action while running in the background
– Alerts and messages can be pushed to apps using push and local notifications
– Apps can complete tasks in the background
• Folders to better organize and access apps
• Home screen Wallpaper*
• Mail improvements
– Unified inbox to view emails from all accounts in one place
– Fast inbox switching to quickly switch between different email accounts
– Threaded messages to view multiple emails from the same conversation
– Attachments can be opened with compatible third-party apps
– Search results can now be filed or deleted
– Option to select size of photo attachments
– Messages in the Outbox can be edited or deleted