News tagged ‘GSM’
Download iOS 7.1 Beta 4 [Links]
UPDATE: Links are deleted after request from Apple.
Developers can download iOS 7.1 Beta 4 . Everybody else can download using the links below.
You can update to iOS 7 without a registered iPhone UDID. Tutorial is here.
Download links for iOS 7.1 Beta 4:
- iPhone
- iPhone 4 GSM 16/32 GB: depositfiles
- iPhone 4 GSM 8 GB: depositfiles
- iPhone 4 CDMA: depositfiles
- iPhone 4S: depositfiles
- iPhone 5 A1428: depositfiles
- iPhone 5 A1429: depositfiles
- iPhone 5C (5.3): depositfiles
- iPhone 5C (5.4): depositfiles
- iPhone 5S (6.1): depositfiles
- iPhone 5S (6.2): depositfiles
Download iOS 7.1 Beta 3 [Links]
Developers can download iOS 7.1 Beta 3 . Everybody else can download using the links below.
You can update to iOS 7 without a registered iPhone UDID. Tutorial is here.
Download links for iOS 7.1 Beta 3:
- iPhone
- iPhone 4 GSM 16/32 GB:
- iPhone 4 GSM 8 GB:
- iPhone 4 CDMA:
- iPhone 4S:
- iPhone 5 A1428:
- iPhone 5 A1429:
- iPhone 5C (5.3):
- iPhone 5C (5.4):
- iPhone 5S (6.1):
- iPhone 5S (6.2):
Download iOS 7.1 Beta [Links]
Developers can download iOS 7.1 Beta . Everybody else can download using the links below.
You can update to iOS 7 without a registered iPhone UDID. Tutorial is here.
Download links for iOS 7.1 Beta:
- iPhone
- iPhone 4 GSM 16/32 GB:
- iPhone 4 GSM 8 GB:
- iPhone 4 CDMA:
- iPhone 4S:
- iPhone 5 A1428:
- iPhone 5 A1429:
- iPhone 5C (5.3):
- iPhone 5C (5.4):
- iPhone 5S (6.1):
- iPhone 5S (6.2):

- iPod
- iPod Touch 5:
- iPad
- iPad 2 Wi-Fi:
- iPad 2 Wi-Fi Rev. A:
- iPad 2 Wi-Fi + 3G GSM:
- iPad 2 Wi-Fi + CDMA:
- iPad 3 Wi-Fi:
- iPad 3 Wi-Fi + 3G GSM:
- iPad 3 Wi-Fi + 3G CDMA:
- iPad 4 A1458:
- iPad 4 A1459:
- iPad 4 A1460:
- iPad mini A1432:
- iPad mini A1454:
- iPad mini A1455:
- iPad Mini Retina Wifi:
- iPad Mini Retina Wifi+LTE:
- iPad Air Wifi:
- iPad Air Wifi+LTE:
 Leave a comment, read comments [3]
Leave a comment, read comments [3]
Apple Announces Unlocked iPhone 5s Availability in 1-2 Weeks
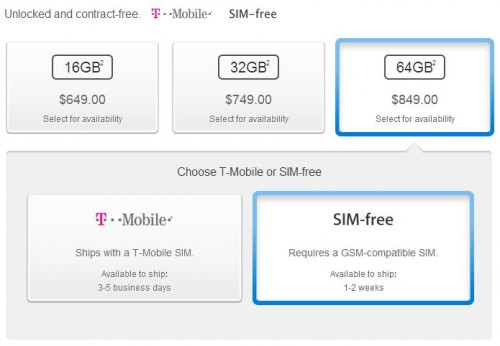
Apple on Friday started offering unlocked, SIM-free iPhone 5s units with shipping estimates of 1-2 weeks. For you to compare - those who decide to purchase the device on contract have to wait for about 3-5 weeks. As to the prices, they’re just the same for both SIM-free and locked smartphones. The iPhone 5s with 16GB of memory on board is available for $649; for the model with 32GB and 64GB of memory one will have to pay extra $100 or $200 respectively.
Apple releases iOS 7.0.4 & iOS 6.1.5 with FaceTime bug fix
Apple has released iOS 7.0.4 for iPhone, iPad, and iPod touch. The update is a bug fix release with improvements. Apple that the update includes a fix for FaceTime calls that could fail for some users. The update is available over-the-air via the Software Update section in the iOS Settings app.
Apple has also iOS 6.1.5 for fourth-generation iPod touch users. That iOS 6 update is designed to fix the FaceTime bug on the non-iOS 7 capable iPod touch.
Direct download links below:
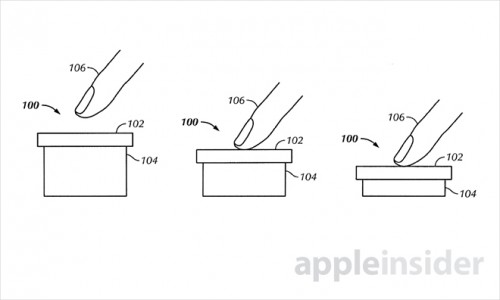
Apple Files Patent for "Touch-Sensitive Depressible Button"
U.S. Patent and Trademark Office published another Apple’s patent application on Tuesday. This time it’s a some kind of touch sensitive button that is capable of detecting multiple levels of pressure. The U.S. Patent No. 8,581,870 is entitled "Touch-sensitive button with two levels".
Here’s what AppleInsider writes:
iPhone 5S and iPhone 5C might support LTE in Russia

iPhone 5S and iPhone 5C will probably support LTE in Russia. According to new Apple smartphones are ready for Russian LTE network. Here is the list of frequencies used by cellular companies:
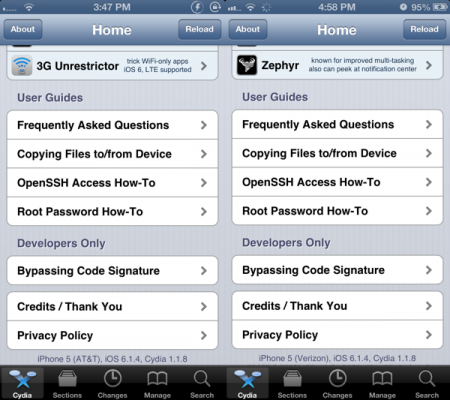
iPhone 5 Running iOS 6.1.4 Jailbroken
If you use a jailbroken iPhone 5, then this article will be interesting for you. Yesterday, a hacker with a nickname winocm announced that he had successfully jailbroken iOS 6.1.4 on his iPhone 5. And this is crucial since this is the first time this firmware version was hacked.
Download iOS 7 Beta 6 [Links]
Developers can download iOS 7 Beta 6 . Everybody else can download using the links below.
You can update to iOS 7 without a registered iPhone UDID. Tutorial is here.
Download links for iOS 7 Beta 6:
- iPhone
- iPhone 4 GSM 16/32 GB:
- iPhone 4 GSM 8 GB:
- iPhone 4 CDMA:
- iPhone 4S:
- iPhone 5 A1428:
- iPhone 5 A1429:
Download iOS 7 Beta 5 [Links]
UPDATE: You can donwload iOS 7 Beta 6 here.
Developers can download iOS 7 Beta 5 . Everybody else can download using the links below.
You can update to iOS 7 without a registered iPhone UDID. Tutorial is here.
Download links for iOS 7 Beta 5:
- iPhone
- iPhone 4 GSM 16/32 GB:
- iPhone 4 GSM 8 GB:
- iPhone 4 CDMA: depositfiles
- iPhone 4S:
- iPhone 5 A1428:
- iPhone 5 A1429:
 Leave a comment, read comments [3]
Leave a comment, read comments [3]
Apple Released iOS 7 Beta 4
Apple iOS 7 Beta 4 is finally released and available for developers. It’s been three weeks since the company from Cupertino unveiled the previous - third - version of its new mobile operating system. Such a long delay is caused by the recent hacker attack on Developer Center.
Download iOS 7 Beta 4 [Links]
Developers can download the beta from . Everybody else can download using the links below.
You can update to iOS 7 without a registered iPhone UDID. Tutorial is here.
Download links for iOS 7 Beta 4:
- iPhone
 Leave a comment, read comments [18]
Leave a comment, read comments [18]
Sim cards can be easily hacked
Karsten Nohl claims that some SIM cards feature a flaw in the encryption technology, so that telephones with the cards can be spied on.
This flaw enables the hackers to send a spoof text message to the device. The latter will answer by revealing the 56-bit data encryption standard key (DES). Using the key, the attacker gains possibility to install dangerous software on the device and even listen in on your phone calls, access/send text messages and much more.
Download iOS Beta 3 [Links]
Developers can download the beta from . Everybody else can download using the links below.
You can update to iOS 7 without a registered iPhone UDID. Tutorial is here.
Download links for iOS 7 Beta 3:
- iPhone
- iPhone 4 GSM 16/32 GB: or
- iPhone 4 GSM 8 GB: or
- iPhone 4 CDMA or
- iPhone 4S: or
- iPhone 5 A1428: or
- iPhone 5 A1429: or
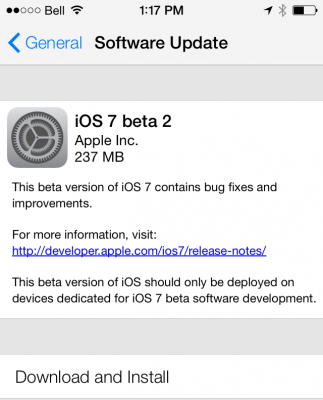
Download links iOS 7 beta 2
Apple released new firmware iOS 7 Beta 2 for developers.
It is available for the following devices: iPhone 5, iPhone 4S, iPhone 4, iPod touch 5G, iPad Mini, iPad 2, iPad 3, iPad 4.
Developers can download the beta from . Everybody else can download using the links below.
 Leave a comment, read comments [6]
Leave a comment, read comments [6]